(Image: Caltech)
Admittedly, it should be clear to everyone by now that “1234” is too weak a password – hopefully. But there are enough other passwords that are far too insecure and are still used.
And as is currently the case in so many areas of technology, the topic of passwords is also being influenced by the current AI boom.
A new study by cybersecurity company Home Security Heroes makes this particularly clear. Around 51 percent of the “conventional” passwords in the training data could be cracked in less than a minute.
How it’s done: PassGAN and RockYou
The security experts used the PassGAN password generator, which is based on the »Generative Adversarial Network« (GAN) based. The network is used to learn from real leaks and create passwords that are as realistic as possible.
Our BY is a machine learning modelwhich pits two neural networks (generator and discriminator) against each other to improve the accuracy of predictions.
The difference between PassGAN and other generators is that the former does not require manual password analysis.
The data comes from a well-known leak from the RockYou company, which was attacked by hackers in 2009. She developed widgets for MySpace and Facebook and lost in the attack 32 million user dataas these were stored in an unencrypted database.
However, “only” 15.6 million passwords were used, as those with fewer than 4 or more than 18 characters were excluded. Unfortunately, the report does not show how large the respective share was.
That’s how (in)secure our passwords are
As mentioned, PassGAN needed for 51 percent of the data, so 8.1 million passwords, not even a minute. In less than an hour it was 65 percent, after just under a day 71 percent and after a month 81 percent.
Of course, the data is from 2009 and we hope that a lot has changed in terms of password security since then, but according to Statista, Germans still use very short passwords. 49 percent use one with 10 characters or fewer.
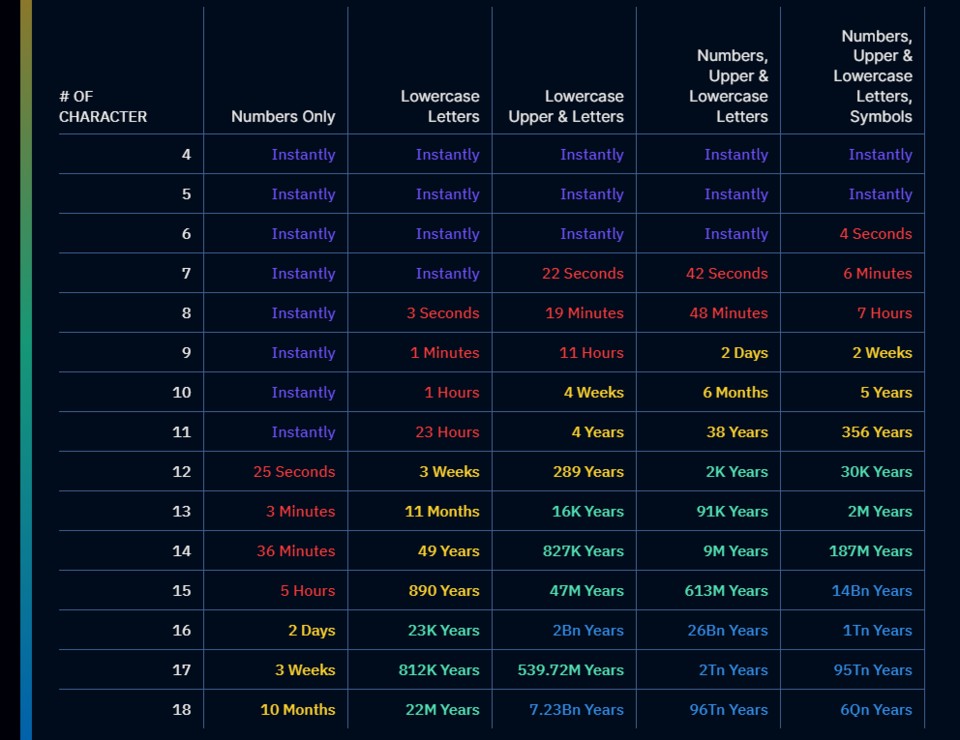
A graphic from the Home Security Heroes shows how unsafe this can be:
The table shows how long it takes to crack passwords with certain lengths and security levels. (Image: Home Security Heroes)
Accordingly, for example, passwords with seven characters, upper and lower case, special characters and numbers in 6 Minutes cracked. The graphic also shows how much more security an additional component gives the password.
For example, adding uppercase and lowercase to a simple ten-character password jumps the time it takes to crack it from one hour to 4 weeks. With the same number of characters and all possible safeguards, it’s five years.
How secure should my password be?
According to the Home Security Heroes, a password should have at least 15 characters. Below that should be two uppercase and two lowercase letters, a number and a special character – at least. The more variety the better.
Given the current state of technology, a password with this strength needs around 14 billion yearsto be cracked.
How secure are your passwords? Do you have to reconsider when you see the table? When was the last time you tinkered with your passwords? Do you use password managers? If yes, which? Have you ever had an account hacked? Let us know your opinions and experiences in the comments!




 The SPARC fusion reactor is the infrastructure of the future for the AI era
The SPARC fusion reactor is the infrastructure of the future for the AI era Galaxy Tab S10 Lite is really cheap right now
Galaxy Tab S10 Lite is really cheap right now Why I use a fan in winter and why I especially rely on this model!
Why I use a fan in winter and why I especially rely on this model! Spotify is increasing its prices again in the USA – what that means for us
Spotify is increasing its prices again in the USA – what that means for us Dead Cells Studio surprises with a roguelite insider tip
Dead Cells Studio surprises with a roguelite insider tip